Protect Data. Secure AI.
Lyo™ is an AI-native data defense engineer. It traces every data journey from code to cloud to AI model, tells you what your data is doing, who is accessing it, and why. Then it empowers you to act before incidents happen.


Trusted by security teams at












































































Visibility without context is just a more expensive alert queue.
Every tool can scan. The question is whether you understand what your data is doing after you find it. That requires context no scanner was built to deliver.
Data is now instruction
Your data shapes what your AI does, what decisions it makes, what it tells your customers. If you don't understand your data's behavior, you don't understand your software.
Software now has agency
AI agents learn, adapt, and act on their own. They don't behave the same way twice. Deterministic security tools cannot protect non-deterministic systems.
Discovery is a feature, not a strategy
Knowing sensitive data exists in Snowflake is step one. Knowing which AI agent can reach it, through what identity, for what business purpose, and whether that combination violates a policy is what actually protects you.
The math doesn't scale
Scanners find problems. Humans fix them. More data, more AI, more problems, more humans needed. You need an engineer that understands the full context and acts on it.
Scanning is not understanding.
Other tools can tell you what data exists and where it sits. Relyance AI tells you the story: what it's doing, who's involved, why it matters, and what to do about it.
Plain English in.
Full context out.
No query builder. No dashboard filtering. Ask Lyo™ a question and get the complete context chain: what's wrong, why it matters, who's involved, what regulation applies, and how to fix it.
Which AI agents can reach customer PII in production?
Show me all data flowing to unapproved third parties
What changed in our data flows since Tuesday?
Are we GDPR Article 30 compliant right now?
.webp)
Data security. AI security. Privacy. Unified.
One intelligence replacing three separate tool stacks.
Data security expert
Discovers and classifies sensitive data across code, cloud, SaaS, and AI systems. Detects exfiltration, shadow data, and misconfigurations continuously.
- Multi-point discovery: code, runtime, data stores, SaaS
- Identity-to-data access path mapping
- Pipeline-aware drift and misconfiguration detection
AI security expert
Maps your full AI footprint. Surfaces compound risks where overprivileged agents intersect with sensitive data through identity intelligence.
- Unified AI and non-AI asset inventory
- MCP server discovery and risk assessment
- Shadow AI detection and onboarding
Privacy expert
Automates data mapping, consent, DSRs, RoPA, and privacy assessments. Turns weeks of manual work into minutes. Stays current as systems change.
- Dynamic ROPAs from continuous code scanning
- DSR fulfillment in minutes, not weeks
- Auto-filled DPIAs, TIAs, and vendor reviews
Real-time data flow intelligence. Code to cloud to AI.
The Data Exposure Graph connects data sensitivity, identity permissions, and AI agent behavior to surface compounding threats that only emerge when you understand the full context.
What security leaders say
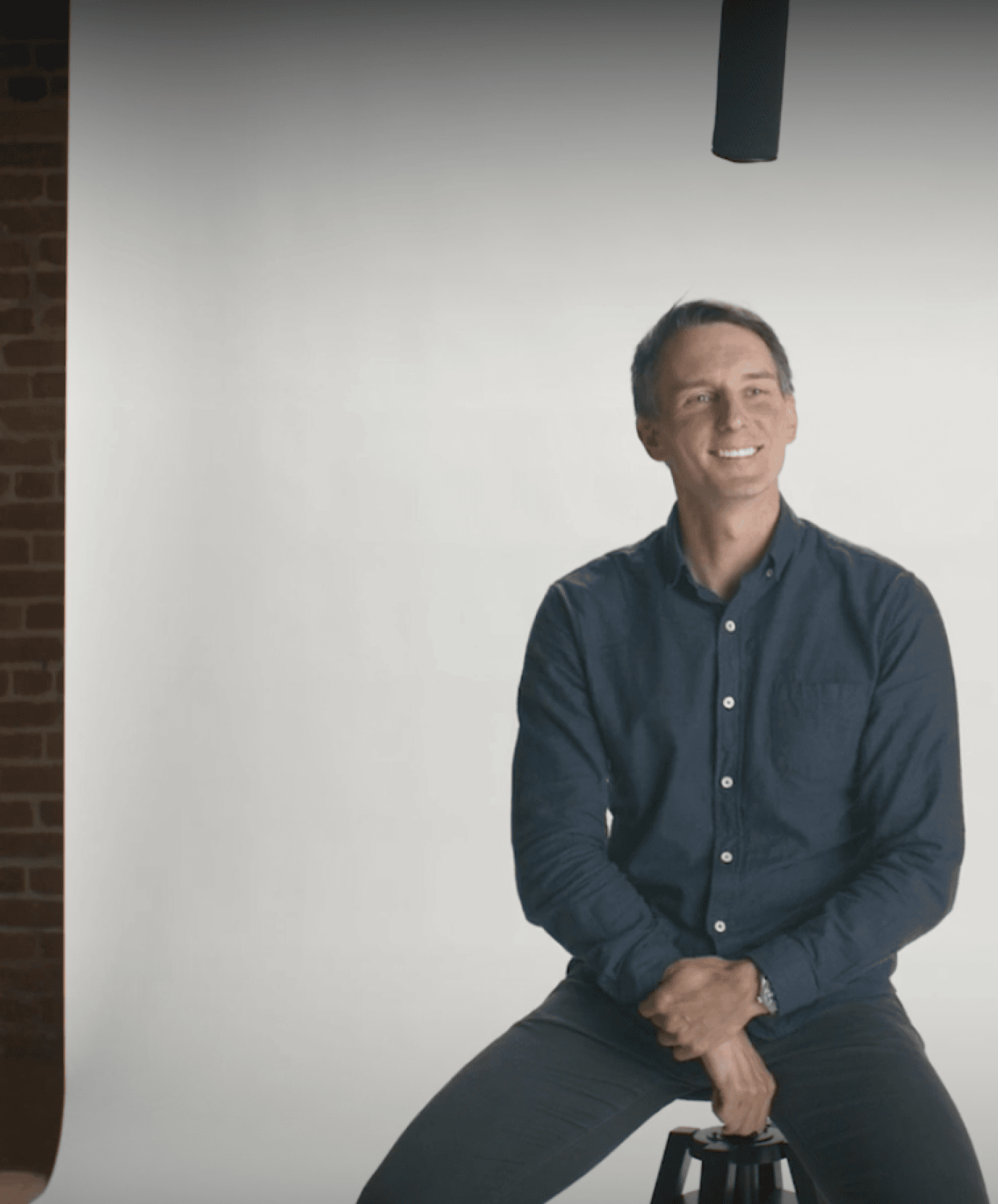

“AI is creating and moving data faster than any team can track. Only AI-native tools like Relyance AI can keep up with the discovery and enforcement loop.”
Chris Bender, CISO
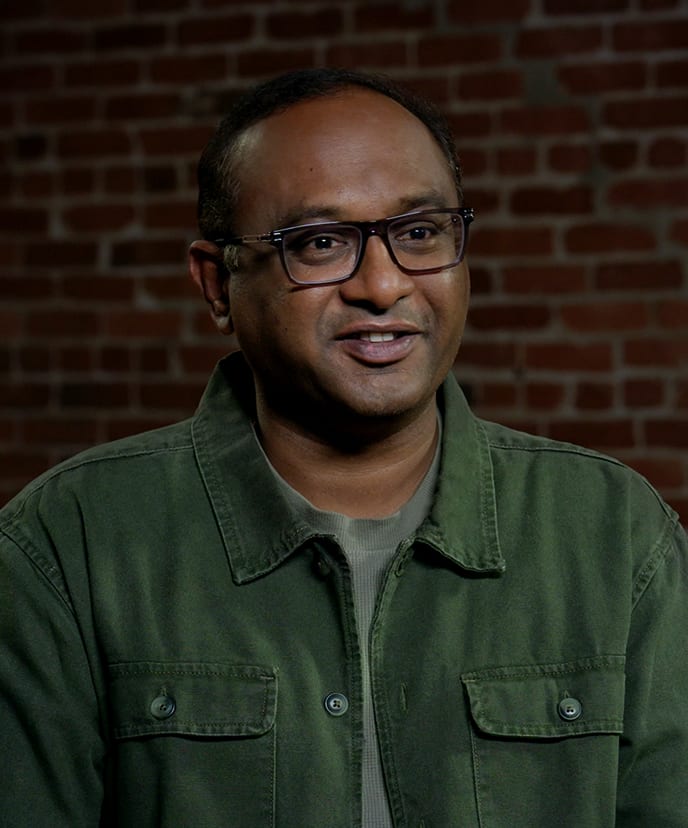

“Most tools show me a snapshot. Lyo™ gives me the full movie, around the clock. I can't afford to choose between innovation and security.”
Karthik Chakkarapani, SVP & CIO


“Relyance gives us a complete, contextual understanding of our data landscape. We can see what we have, how it's used, who owns it, and where the risks are. This level of clarity is strengthening our overall security posture.”
Jason James, CIO
You may also like

Privacy in the trenches: What we learned (and what we laughed about) at IAPP Global Summit

RSAC™ 2026 Conference recap: Securing AI starts with understanding your data
